Investing in your cybersecurity won’t make you any money. Discover 3 good reasons to change your point of view: Crisis, Compliance and Consciousness.
Improving the security of information systems does not save money. However, a major security incident will certainly cause a major loss of profit.

So what motivates an organization to measure, prioritize, and implement IT security measures?
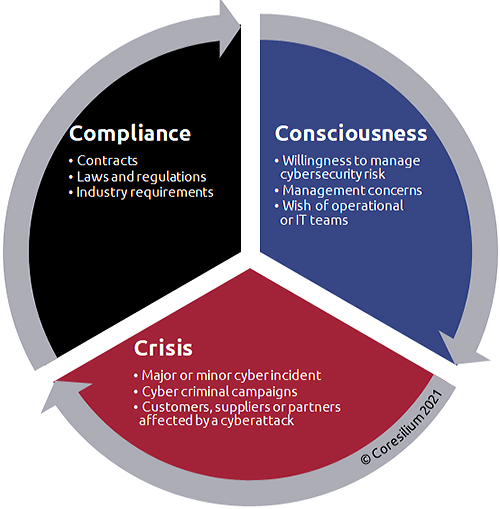
Here are the 3Cs that summarize the main drivers: Crisis, Compliance and Consciousness. Each category demonstrates an increasing maturity.
Strengthening cybersecurity following a crisis
In many cases, the occurrence of a security incident is the trigger. As soon as the company enters emergency mode, it must recover and restore all affected systems. Then, it implements the necessary security measures in a reactive manner. Indeed, if an organization restores vulnerable systems, it is only a matter of time before they are compromised again.
Stakeholders (customers, shareholders, partners) also want to see the company take responsibility and correct its vulnerabilities. The managers of the company must then justify concrete means and action plans.
From my experience, it is more expensive to set up security projects in an emergency than to plan them. Under pressure, employees must accept more restrictive security controls. Because the security incident justifies these measures, the usability of the systems can then deteriorate and productivity decline.
In short, the crisis is still too often what pushes an organization to put in place security measures.
Meet compliance requirements
Deploying security controls through compliance is an approach that remains quite reactive. Indeed, actions are taken when the company is obliged to comply with a contractual, regulatory or industry requirement.
For example, a tender may contain specific data protection requirements or standards. Often, it is a new regulation that forces organizations to comply. Growth in new regulated markets may also require the establishment of security control frameworks.
In addition, we must not forget that an organization can be compliant without being safe. Compliance control frameworks are most often tactical and not aligned with corporate strategy. Due to the dynamic nature of cyber risks, compliance requirements are generally exceeded when approved and made mandatory.
However, compliance is an excellent starting point for implementing security measures and includes a financial motivation (loss or gain of a contract, fines following a conviction).
Being conscious of the risk
The awareness is indicative of a decision to manage cybersecurity risk, just like other risks in the organization.
The initial request can come from the technical and operational teams who fear an incident. But more and more often, it is the leaders who express the will to measure, prioritize and reduce the security risk. Sometimes, in a process of transferring risk to an insurer (cyber insurance), the organization must justify an action plan and improve security measures.
This conscious and risk-based approach is the most effective. Since leaders are aware of risk, they promote secure behaviours and actions. Corporate culture evolves by integrating the necessary measures. The organization can then anticipate, align, prepare and implement its security master plan. And this also includes a security incident response plan to deal with a possible crisis!
As with any event, being conscious of risk gives you a head start. Regulatory approaches, which require the organization to take action, or corrective action following an incident, are less effective and more costly.
How do you see cybersecurity in your organization? Are you proactive or reactive?